This week is big not just for UK politics but also for conferences exploring how Biometrics and digital Identity can be used positively by society. Kicking off the first in-person (and online) hybrid conference on these themes, The Biometrics Institute’s annual London Congress started yesterday.
As biometrics becomes increasingly pervasive, what has changed in a year?

Adoption of biometric systems
The use of biometrics as a key enabler for Digital Identity is unsurprisingly top of the change agenda for both industry professionals and clients, which manifests itself across technical, regulatory and other areas. The EU is again leading regulatory progress globally with the European Digital-ID Framework1 proposals (also known as “e-ID 2.0” or EIDAS 2.0”) that will allow citizens across the continent to easily verify their ID, access public and private services and store sensitive digital documents in one place. Like the UK’s digital identity and attributes trust framework2, it is intentionally technology agnostic, but as the component technologies for e-ID grown in number and sophistication, how will regulators, legislators and the public react to new forms of Artificial Intelligence, Digital Wallets, Payments, Driving Licence re-use and more?
Bringing the issues to focus is the commencement of four consortia for live testing across EU countries. For example, the announcement that a six-country consortium of trusted identity providers led by NOBID3 (Nordic-Baltic eID Project) proposes to deliver a large-scale, cross-border payments pilot strongly aligned with the aims of e-ID’s digital identity wallet. Having well-established digital infrastructures, following its successful harmonisation of several national eID programs comprising tens of millions of European citizens, the group will “collaborate to show how payments and ID can be combined effortlessly, across borders and in multiple currencies.”
Fears and misconceptions
Meanwhile the largest drawbacks to faster and wider adoption of biometrics are public trust and legislation (often linked to trust/privacy issues), together with governance and misinformation. Calls to ban facial recognition, particularly for uses such as mass surveillance, social media political use and school administration, are gaining traction, emphasising the need for strong oversight underpinned by a consensus-based ethical framework. Claims of election manipulation abound (not without cause) and concerns about public deceit and individual fraud increase as the technologies develop. The Congress gives insiders the chance to explore the speed and types of progress, together with discussing responsible management and potential exclusion areas.
During the 2021 Congress, FX artist Chris Ume demonstrated Deep Fake current capabilities for both video and voice with compelling Tom Cruise4 and other impersonations.
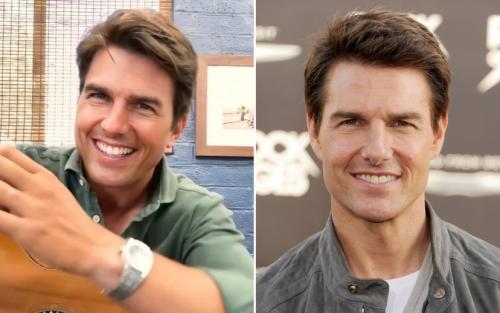
Spot the fake Tom Cruise
Since film and TV have increasingly incorporated such tech. There are storylines such as the hero seeking to expose ‘seeing is believing’ malpractice by dramatically educating the public (eg BBC’s The Capture). In reality, Series 2’s portrayal of intercept manipulation of live video image and audio feeds for transmission across secure networks would need software and computing resources to be substantially transformed to get anything close to the real-time scenarios shown.

Deep fakes mean Security Minister's job loss (The Capture)
Real time image and voice manipulation at a high enough quality to fool most professionals is not yet here. It currently takes an expert like Chris Ume 2-3 months training his computer model and 1 hour of post-production per 1 sec video (fixing flaws frame by frame), even when using ‘likeness’ actors to make the task easier. Advances in software techniques and quantum computing performance will reduce this, meaning that in most of our lifetimes such power may be a future reality. Importantly we have time to prepare, educate and adjust our reactions as we become more critical over what we see before accepting footage as ‘real or fake’ and as a profession ensure that society learns how to nullify or prevent potential consequences of the capabilities used irresponsibly.
Governance and Education
Societal education and public debate is central to reducing fears and mistrust. But equally the industry also knows that it has to constantly improve its processes and technologies to stay one step ahead of fraudsters.
Multi-modal and Behavioural biometrics are increasingly favoured by thought leaders in the biometrics community, since it’s long been known that multiple identity factors are better than one and that human behaviour is the hardest to fake. Here the difficulty level depends upon the type of technology ranging from keyboard interactions to biometric digital handwritten signatures.
Work to mitigate against this and related challenges is already underway in the Biometrics and Trust communities. The Biometrics Institute published its Three Laws of Biometrics5 to open its 2020 Online Congress and the latest member survey shows strong agreement (81%) that ‘no biometric system should operate totally independently of human oversight’, i.e. there should be a ‘human in the loop’, especially in the context of using live facial recognition. This does not mean for every transaction, but certainly for transactions where the confidence level deriving from the biometrics themselves and associated data falls below the require threshold for the transaction type to be validly approved.
There is also debate about how citizens can know whether they can trust information seen. This debate is not only at the conferences but also between the EU and US big tech concerning matters such as the EU’s Qualified Web Authentication Certificates aimed to secure and identify websites.6
In medieval times, wax seals issued by a tightly controlled group and legally protected were used to assure trust to a remote recipient. Digital equivalents are now available in the form of Qualified Certificates, which can be deployed to protect and assure websites, emails, documents and other information formats. These are issued by a small number of regulated (or “Qualified”) providers known as Qualified Trust Services Providers (QTSPs). After inspecting and verifying identity of a person or organisation, a QTSP can issue one of various forms of ‘tokens’ (digital hash code) which can be embedded in encrypted communications. For ‘legal persons’, i.e. organisations, these are referred to as “eSeals”. These can provide additional assurances such as time stamping and location checking.
Permitted Data Exchanges
Concerns also exist around personal data sharing. Here the world of Open Data regulation shows the way. Examples include the implementation of the UK’s Open Banking initiatives that has enabled many financial services companies to innovatively offer consumer convenience with productivity, with emerging regulator involvement across many other sectors like insurance, utilities and the like. Financial data, like biometric data, is naturally sensitive but when stripped of many associated data points can become sufficiently anonymised for use to increase security and insights – ones valuable to the consumer.
This week also sees conferences by other significant players like the Open Identity Exchange (OIX), formed to collaborate and develop the guidance needed for inter-operable trusted identities, who have increasingly supported education concerning the linkages between digital signatures and digital identity verification. Trusted chains and use of robust certification enable ‘Yes/No’ answers to remotely communicated questions such as ‘does the biometric data profile match the trusted data profile claimed as held by the consumer’s bank?’

This ‘federated identity’ practice may be just a fraction of the biometric and identity dataset collected upon presentation when requesting verification, using anonymised codes for the encrypted communications between the bank (or other third party trusted entity) and the processor’s application (e.g. a health or welfare authority, insurer, product seller, etc.). This means that the user controls what data they choose to share on a case-by-case basis.
So what?
Just as Biometrics are a key enabler for Digital Identity, Digital Identity done right enables higher trust levels providing multiple benefits to modern societies. Remote, secure and convenient identity verification using multi-modal biometrics and selective data exchange enables the removal of inefficient practices (e.g., those mandating paper or clunky electronic processes) for individual transactions, replacing them instead with fast, intuitive ways to assure identity in a consumer and planet friendly way.
Beyond this, biometrics and digital identity can provide the levels of assurance when remotely connected that enable us to trust each other more and also to accept mass decisions as democratic – and these benefits are invaluable.
----------------------
Footnotes:
1. European Digital-ID Framework, also known as “e-ID 2.0” or eIDAS2”, enables self-determined personal digital wallets that would allow for secure and easy access to different services, both public and private, under the user’s full control”. The Wallet is a mobile application combined with online platforms. Since data held may include various aspects of personal identifiers (e.g. birth certificates, medical documents, bank accounts, tax returns, education status, prescriptions, etc.), access to this must be securely held and accessed, with sharing of any parts in the data owner’s own control.
2. UK DCMS trust framework is in pilot test phase. The Department for Digital, Culture, Media and Sport’s (DCMS) published its UK Digital Identity and Attributes Trust Framework last year, a set of rules organisations agree to follow to conduct secure, trustworthy identity or attribute checks. There are Right to Work, Right to Rent, and Disclosure and Barring Service’s (DBS) initiatives currently which form part of DCMS’s trust framework’s testing process, and learnings will help to further refine its development.
3. NOBID announced its plans on 14th September that includes its support from leading European providers of banking and payments, including DSGV in Germany, DNB and BankID in Norway, Nets in Denmark, Intesa Sanpaolo, PagoPA and ABILab in Italy and Greiðsluveitan in Iceland. Technology partners participating in the consortium include Thales, iProov, Signicat, RB, Auðkenni, IPZS, Poste Italiane, Intesi Group, InfoCert, FBK and Latvian State Radio and Television Centre. Merchants that will be testing out the payment solution include Elkjøp in Norway and REWE-group in Germany.
The concept of the European digital identity and the development of the digital identity wallet may mark a turning point for trusted service providers in Europe by unlocking new personalised services that will be developed to be cross-border by default, while at the same time solving some of the challenges that all EU countries are facing in the process of implementing the eIDAS requirements like electronic identification (cross-border), identity matching, and compatibility of different service provider solutions across the EU.
4. Tom Cruise impersonations start at 0.50 mins & 3.36 mins, as Chris explains the capabilities and limitations of using the available technologies for video and voice deep fakes.
5. The Three Laws of Biometrics are a prompt to for everyone to remember the fundamentals of using biometric technology responsibly and ethically. The three laws are:
- POLICY – comes first: Any use of biometrics is proportionate, with basic human rights, ethics and privacy at its heart.
- PROCESS – follows policy: Safeguards must be in place to ensure decisions are rigorously reviewed, operations are fair and operators are accountable.
- TECHNOLOGY – guided by policy and process: Know your algorithm, biometric system, data quality and operating environment and mitigate vulnerabilities, limitations and risks.
These laws should be used as a checklist to guide organisations in their implementations, and crucially the order in which tasks should be carried out. Policy first, then process and only when robust review of those initial steps has taken place should the requisite technology be appropriately explored.
6. QWACs amendment to eIDAS Article 45 covers the EU’s Qualified Web Authentication Certificates (“QWACs"). These certificates are used to secure and identify websites for the necessary level of EU consumer protection. However EU interests are being forced to defend their position by railing against misinformation campaigns by Mozilla/Goggle attempting to promote their commercial interests. More here.
The Author: Chris Jones is the Managing Director of Icon UK Limited, a specialist in document-based information and identity. Icon is a member of various industry bodies and provides trusted identity and information solutions to businesses and the UK public sector. Chris is an active contributor to innovations in legal and regulatory acceptance of eSignatures, eSeals and eDocuments, including Reports by the Law Commission and the Ministry of Justice on electronic execution of eSignatures and documentation.
. | 

 Connect with us on Linkedin
Connect with us on Linkedin 


 Connect with us on Linkedin
Connect with us on Linkedin 

![]()
![]()
![]()